#nginx環境下での証明書取得手順(Apacheの場合は「--apache」)
[root@ufuso ~]# /usr/local/bin/certbot-auto --nginx
Bootstrapping dependencies for RedHat-based OSes that will use Python3… (you can skip this with –no-bootstrap)
…
…
…
インストール 38 パッケージ
ダウンロードサイズの合計: 44 M
インストール済みのサイズ: 108 M
#「y」入力
これでよろしいですか? [y/N]: y
…
…
…
インストール済み:
gcc-8.2.1-3.5.el8.x86_64
python3-virtualenv-15.1.0-18.module_el8.0.0+33+0a10c0e1.noarch
python36-devel-3.6.8-2.module_el8.0.0+33+0a10c0e1.x86_64
redhat-rpm-config-116-1.el8.0.1.noarch
libffi-devel-3.1-18.el8.x86_64
openssl-devel-1:1.1.1-8.el8.x86_64
annobin-8.64-1.el8.x86_64
cpp-8.2.1-3.5.el8.x86_64
dwz-0.12-9.el8.x86_64
efi-srpm-macros-3-2.el8.noarch
ghc-srpm-macros-1.4.2-7.el8.noarch
go-srpm-macros-2-16.el8.noarch
isl-0.16.1-6.el8.x86_64
ocaml-srpm-macros-5-4.el8.noarch
openblas-srpm-macros-2-2.el8.noarch
perl-srpm-macros-1-25.el8.noarch
platform-python-devel-3.6.8-4.el8_0.x86_64
python-rpm-macros-3-37.el8.noarch
python-srpm-macros-3-37.el8.noarch
python3-rpm-generators-5-4.el8.noarch
python3-rpm-macros-3-37.el8.noarch
qt5-srpm-macros-5.11.1-2.el8.noarch
rust-srpm-macros-5-2.el8.noarch
glibc-devel-2.28-42.el8.1.x86_64
glibc-headers-2.28-42.el8.1.x86_64
kernel-headers-4.18.0-80.11.2.el8_0.x86_64
keyutils-libs-devel-1.5.10-6.el8.x86_64
krb5-devel-1.16.1-22.el8.x86_64
libcom_err-devel-1.44.3-2.el8.x86_64
libkadm5-1.16.1-22.el8.x86_64
libselinux-devel-2.8-6.el8.x86_64
libsepol-devel-2.8-2.el8.x86_64
libverto-devel-0.3.0-5.el8.x86_64
libxcrypt-devel-4.1.1-4.el8.x86_64
pcre2-devel-10.32-1.el8.x86_64
pcre2-utf16-10.32-1.el8.x86_64
pcre2-utf32-10.32-1.el8.x86_64
zlib-devel-1.2.11-10.el8.x86_64
完了しました!
Creating virtual environment…
Installing Python packages…
Installation succeeded.
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator nginx, Installer nginx
#有効期間切れを事前に通知してもらうためにメールアドレスを入力
Enter email address (used for urgent renewal and security notices) (Enter ‘c’ to
cancel): tu@ufuso.jp
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
Please read the Terms of Service at
https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf. You must
agree in order to register with the ACME server at
https://acme-v02.api.letsencrypt.org/directory
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
#同意書なので「A」を入力
(A)gree/(C)ancel: A
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
Would you be willing to share your email address with the Electronic Frontier
Foundation, a founding partner of the Let’s Encrypt project and the non-profit
organization that develops Certbot? We’d like to send you email about our work
encrypting the web, EFF news, campaigns, and ways to support digital freedom.
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
#内容を知らないので私は「N」を入力
(Y)es/(N)o: N
Which names would you like to activate HTTPS for?
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
#あなたのドメイン名が表示されるので、その中からひとつを番号入力
1: ufuso.dip.jp
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
Select the appropriate numbers separated by commas and/or spaces, or leave input
blank to select all options shown (Enter ‘c’ to cancel): 1
Obtaining a new certificate
Performing the following challenges:
http-01 challenge for ufuso.dip.jp
Waiting for verification…
Cleaning up challenges
Deploying Certificate to VirtualHost /etc/nginx/nginx.conf
Please choose whether or not to redirect HTTP traffic to HTTPS, removing HTTP access.
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
1: No redirect – Make no further changes to the webserver configuration.
2: Redirect – Make all requests redirect to secure HTTPS access. Choose this for
new sites, or if you’re confident your site works on HTTPS. You can undo this
change by editing your web server’s configuration.
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
#強制的に暗号通信を行う設定の2を入力
Select the appropriate number [1-2] then [enter] (press ‘c’ to cancel): 2
Redirecting all traffic on port 80 to ssl in /etc/nginx/nginx.conf
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
#以下の表示が出れば取得は成功
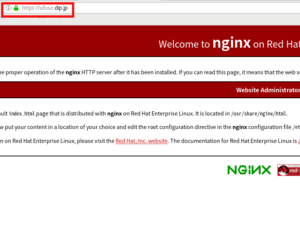
Congratulations! You have successfully enabled https://ufuso.dip.jp
You should test your configuration at:
https://www.ssllabs.com/ssltest/analyze.html?d=ufuso.dip.jp
– – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – – –
IMPORTANT NOTES:
– Congratulations! Your certificate and chain have been saved at:
/etc/letsencrypt/live/ufuso.dip.jp/fullchain.pem
Your key file has been saved at:
/etc/letsencrypt/live/ufuso.dip.jp/privkey.pem
Your cert will expire on 2020-02-25. To obtain a new or tweaked
version of this certificate in the future, simply run certbot-auto
again with the “certonly” option. To non-interactively renew *all*
of your certificates, run “certbot-auto renew”
– Your account credentials have been saved in your Certbot
configuration directory at /etc/letsencrypt. You should make a
secure backup of this folder now. This configuration directory will
also contain certificates and private keys obtained by Certbot so
making regular backups of this folder is ideal.
– If you like Certbot, please consider supporting our work by:
Donating to ISRG / Let’s Encrypt: https://letsencrypt.org/donate
Donating to EFF: https://eff.org/donate-le
#nginx.confファイルが自動で書き換えられたので、nginxを再起動
[root@ufuso ~]# systemctl restart nginx |
コメントを残す